Identity & Access
Your people, your rules
Enterprise identity management
Connect to your existing identity infrastructure — Active Directory, Entra ID, LDAP — with fine-grained permissions that protect without obstructing.
Directories
Connect your existing
identity fabric
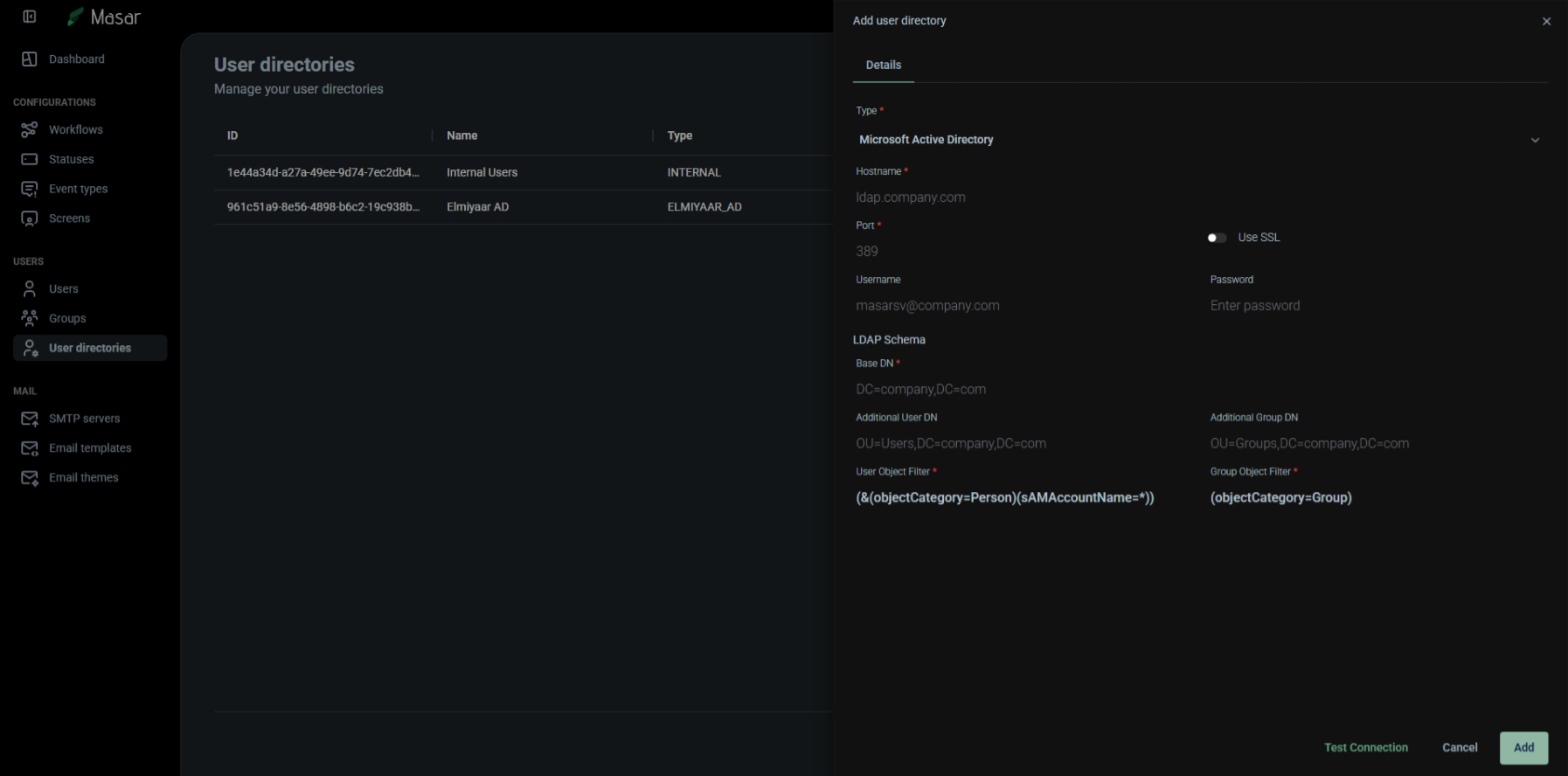
Masar doesn't ask you to recreate your user directory. It connects to what you already have — syncing users, groups, and organizational structure directly into the workflow engine. Multiple directories can run simultaneously, each with its own capabilities and sync schedule.
Microsoft Active Directory
Full LDAP schema support with custom user and group object filters, base DN, and additional DN configuration
Microsoft Entra ID
Cloud-native identity for modern hybrid environments — sync from your Azure AD tenant
Multiple Directories
Internal, Active Directory, LDAP, and Entra ID — running simultaneously with per-directory capability flags
Permissions
Precision access
at every level
The permission model is built for enterprise complexity. Resource-based permissions with action-level granularity, assigned through groups. Users inherit permissions through group membership, with caching for performance and consistency.
10 Permission Actions
READ, CREATE, UPDATE, DELETE, ADMIN, MANAGE_OWN, READ_OWN, UPDATE_OWN, DELETE_OWN, TEST
Group-Based Access
Assign permissions to groups, users inherit through membership — multi-group support with caching
Manager Hierarchy
User profiles support manager relationships — enabling hierarchical approvals and escalation paths
Security
Enterprise-grade protection
Authentication
JWT tokens, API tokens, TOTP (2FA), presigned URLs — multiple authentication methods for every scenario
Encryption
Password hashing with salt, SMTP credential encryption with IV, encrypted field storage throughout the system
Audit Trail
Every login, logout, password change, permission change, and access denial logged with user, IP, and timestamp
Related Features
Explore more of what Masar offers
Identity that fits your organization
Masar respects your existing infrastructure. Connect your directories, define your rules, and let the engine handle the rest.
Start a conversation